Setting up your integration for Tenable.io
Overview
In order for CyberSystem to access your Tenable Vulnerability Management scanning results, you will need to set up application credentials within Tenable.
Broadly speaking these are the steps that you will need to follow, however please refer to Tenable's own documentation as this process may change from time to time. You will find the relevant links in the sections below.
What does CyberSystem need?
There are three pieces of information that CyberSystem needs to successfully integrate your Tenable Vulnerability Management scanning results into your organisation:
- Access Key
- Secret Key
To obtain this information, you will need to setup a user generate their API key. You can optionally provide more controls by setting up a permission group for that user.
Note, a Name is also needed, however this is a reference only and does not need to match any information within Tenable itself.
Setup within Tenable
It is very likely that you already have users and permission configurations already created within your Tenable instance. If you are going to use one of these users for the integration it is important to review how the user is setup and make sure that it has the appropriate permissions mentioned below.
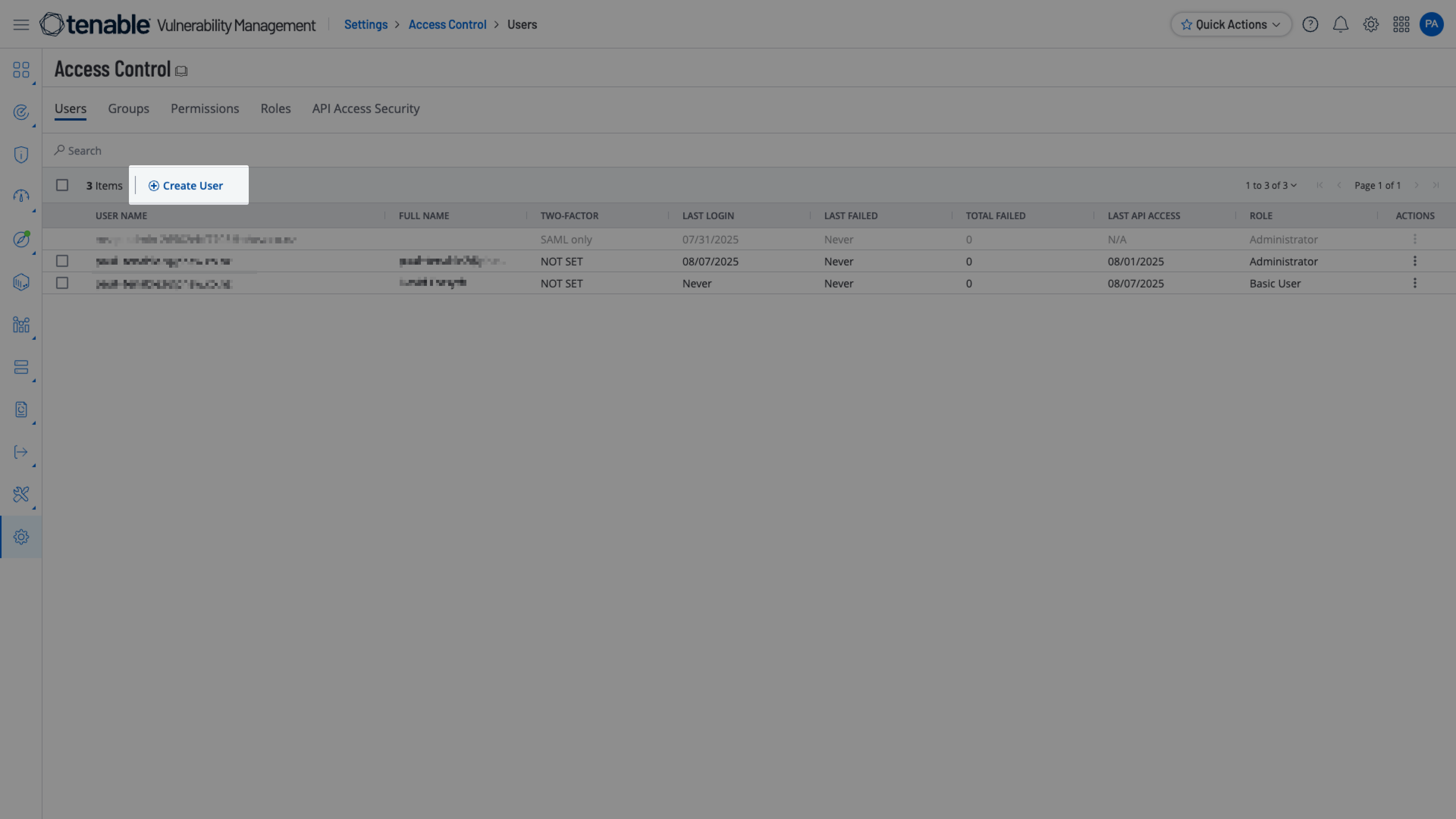
Setting up a user
Tenable documentation: Settings >Account Management > Access Control > Users
Adding a user requires you to open Access Control and click the Create User link, then follow the instructions.
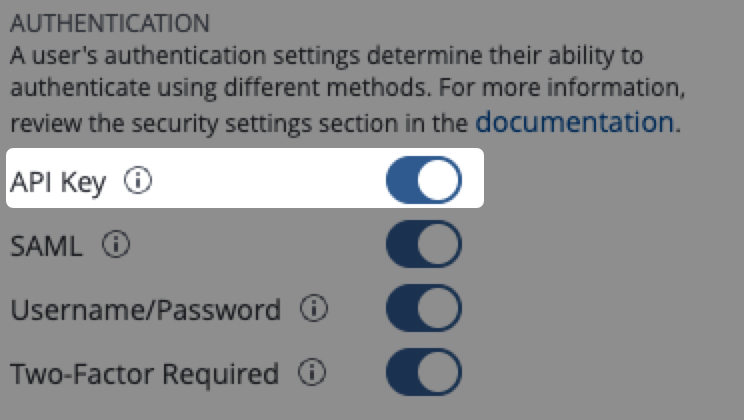
It is important that the API Key toggle is kept ON:
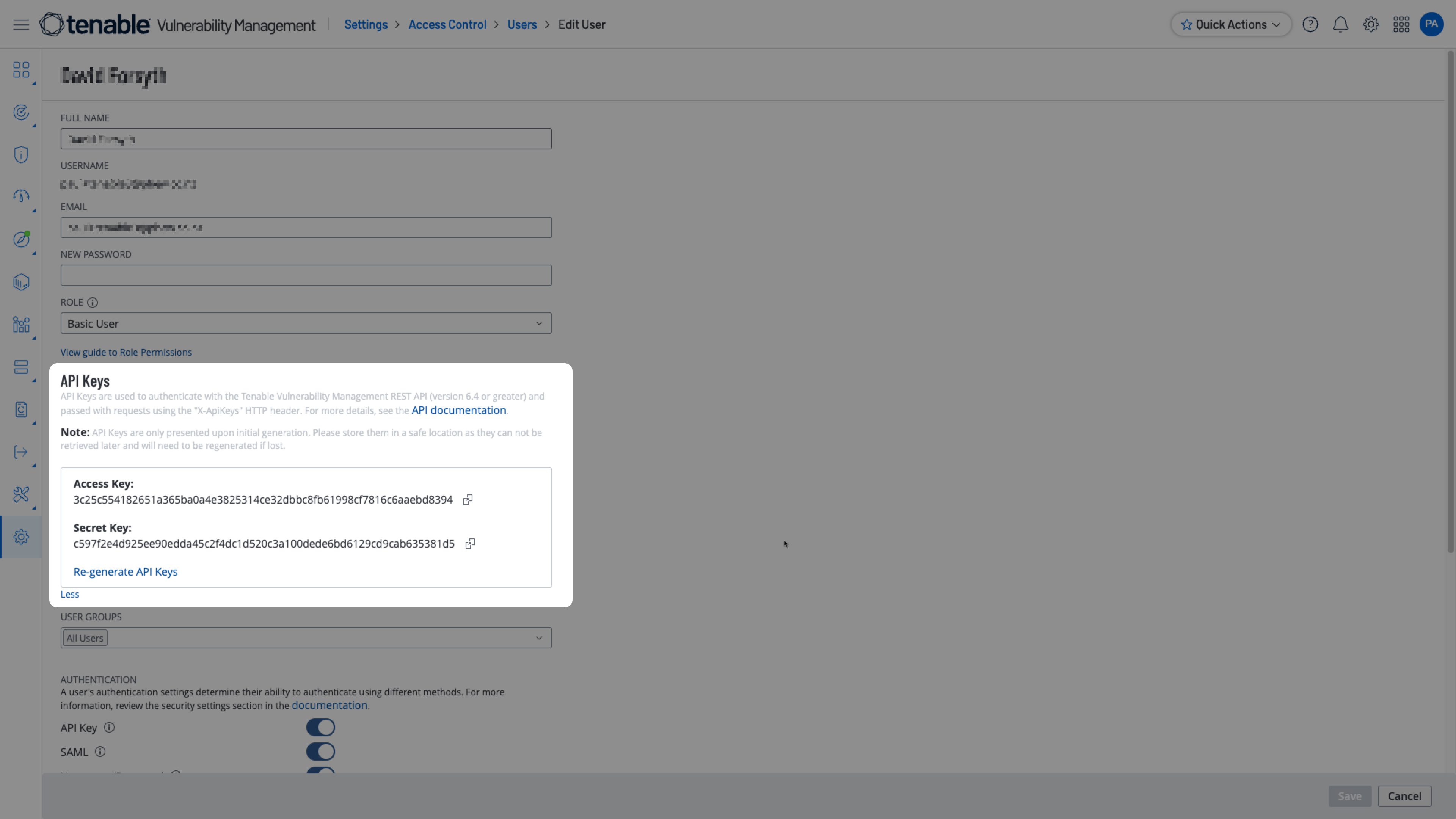
Setting up an API Key
Tenable documentation: Generate another user's API Keys
This is accessed via editing the users details.
- Click on the user that you have configured
- Click "More" in the API Keys section:

3. Generate (or re-generate) the keys. These are what you need to put into CyberSystem when setting up the integration.
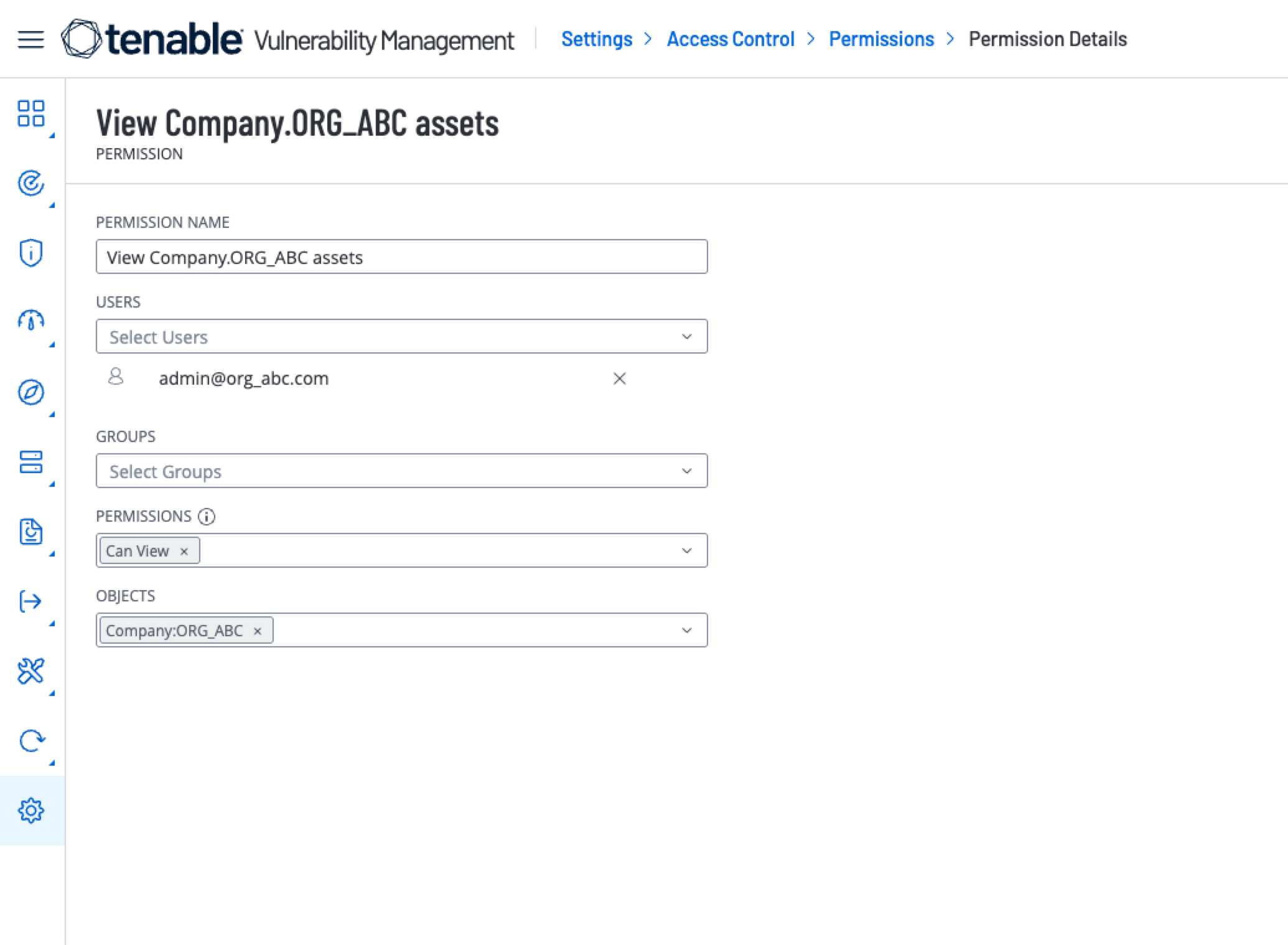
Setting up a permission configuration (optional)
Tenable documentation: Creating and Add a Permission Configuration
Setting up and assigning a permission configuration to apply to this user can be helpful, depending how you have configured your Tenable scans.
For example, if you only want to expose certain asset tags to CyberSystem, this can be done by creating a permission configuration that can only be seen by the user used for the integration.
To do this, simply navigate to the Permissions tab of the Access Control page, add a new permission and follow the in-app wizard.
If there was a Company asset tag for ORG_ABC, then the permissions setup would look like the following:
Where do the keys go?
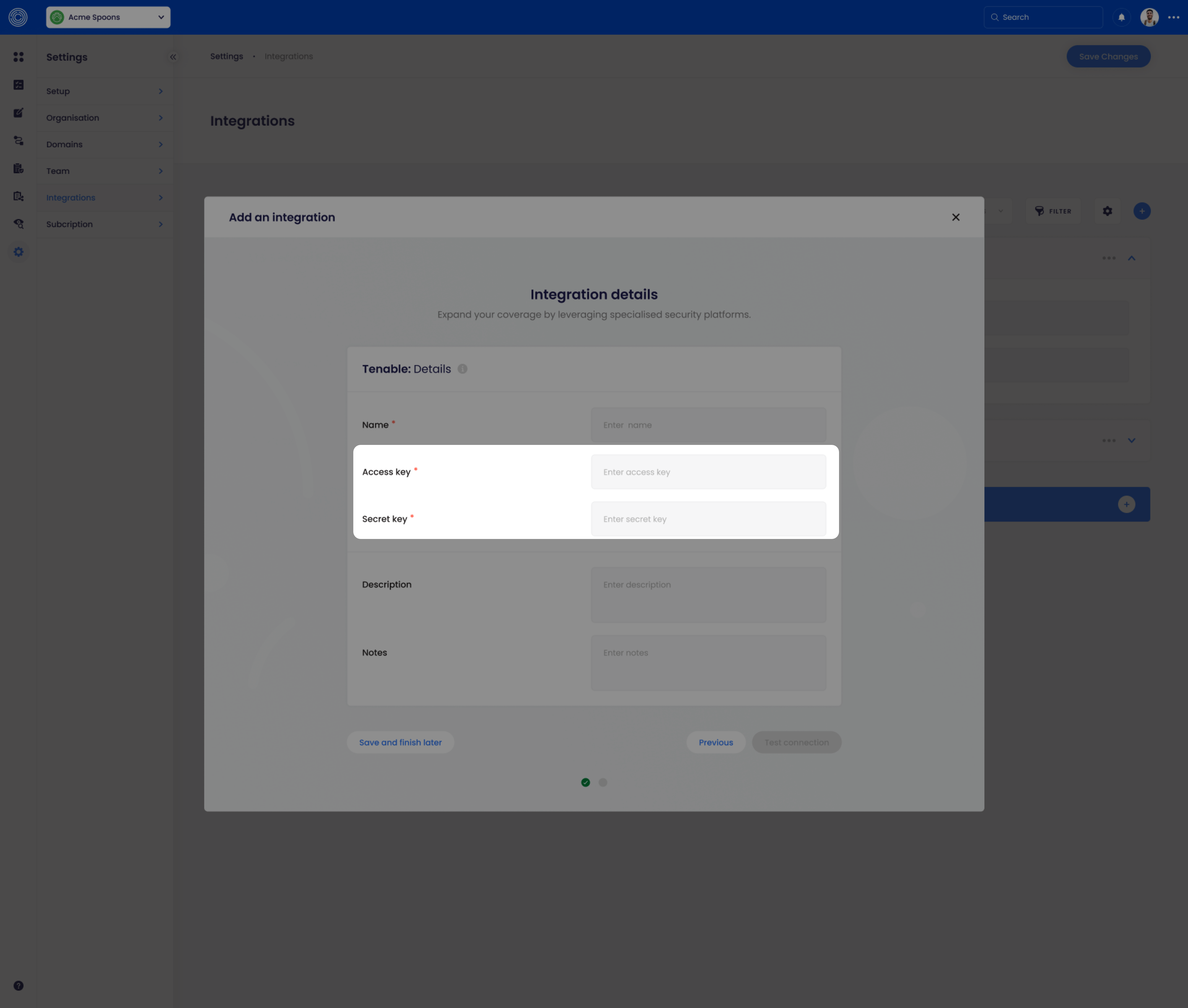
When creating a new Tenable integration from the Settings > Integration page within CS, you will be presented with a form to place these keys:
Next steps
Setup your integration and want to start exporting data into CyberSystem? Head to the Scanning > Tenable.io: Exports page.